Secure and Comply AcrossYour Kubernetes EnvironmentsContinuously
Kubernetes has become the backbone of modern cloud-native applications—but it has also introduced a new class of security and compliance risks. Suronex helps organizations secure and govern Kubernetes environments with continuous compliance, real-time visibility, and intelligent remediation, without slowing development velocity.
The Problem:
Kubernetes Changes Faster Than Compliance
Misconfigured APIs, overly permissive RBAC, exposed services, and vulnerable container images continue to be leading causes of cloud-native incidents. Recent industry incidents and disclosures (2024–2025) involving Kubernetes API exposure, insecure workloads, and compromised container images across managed Kubernetes platforms have reinforced a hard truth: Kubernetes security failures are rarely zero-day exploits—they are configuration failures.
Security Teams Face:
Modern Kubernetes environments—across Amazon EKS, Azure AKS, and Google GKE—are highly dynamic. Clusters, pods, namespaces, identities, and network policies change constantly, making manual audits and point-in-time checks ineffective.
Limited visibility into cluster configurations and access paths
Over-privileged service accounts and RBAC roles
Vulnerable container images deployed across multiple clusters
Difficulty maintaining compliance with CIS and regulatory standards
How Suronex Solves Cloud-Native Compliance
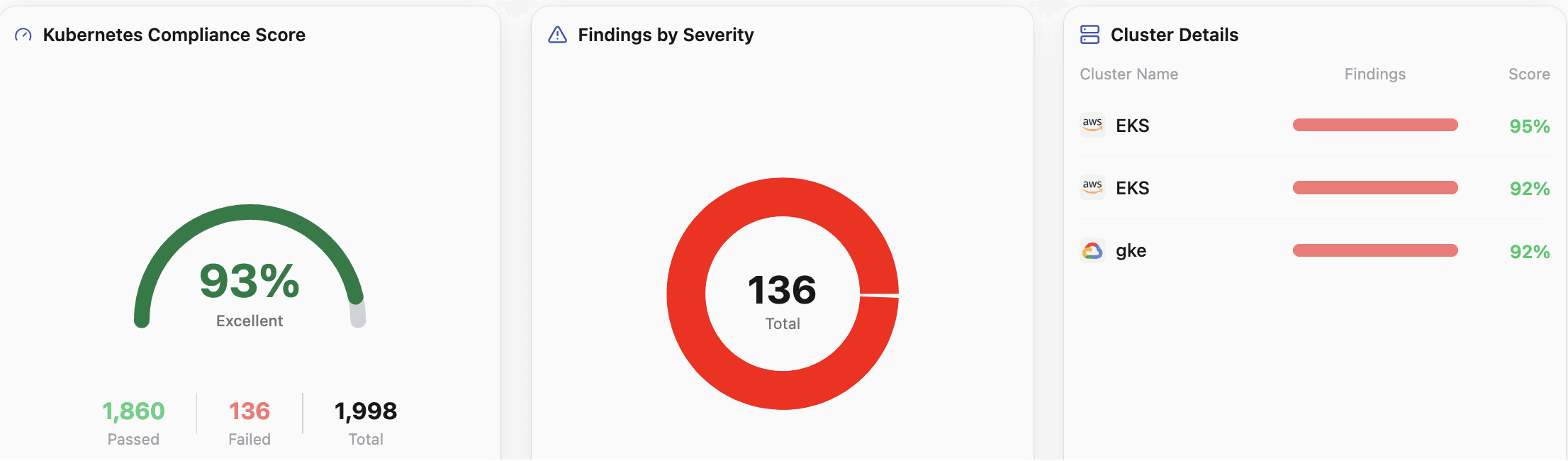
Suronex delivers Kubernetes Security Posture Management (KSPM) and Cloud-Native Compliance in a single, unified platform. Within minutes, Suronex maps your Kubernetes environments, continuously scans for misconfigurations, and enforces compliance aligned with industry benchmarks.
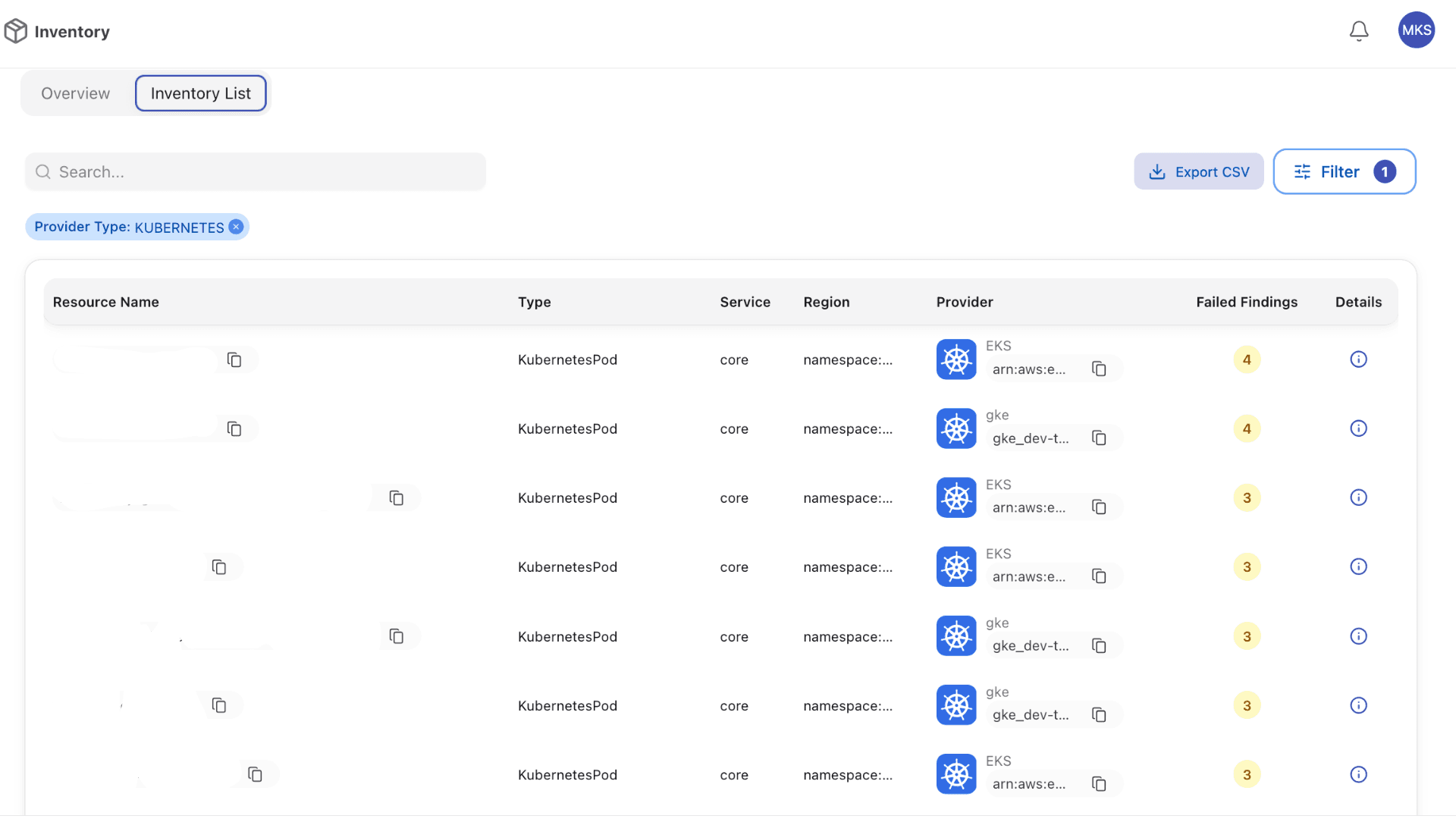
Complete Visibility
Complete Visibility
Across Kubernetes
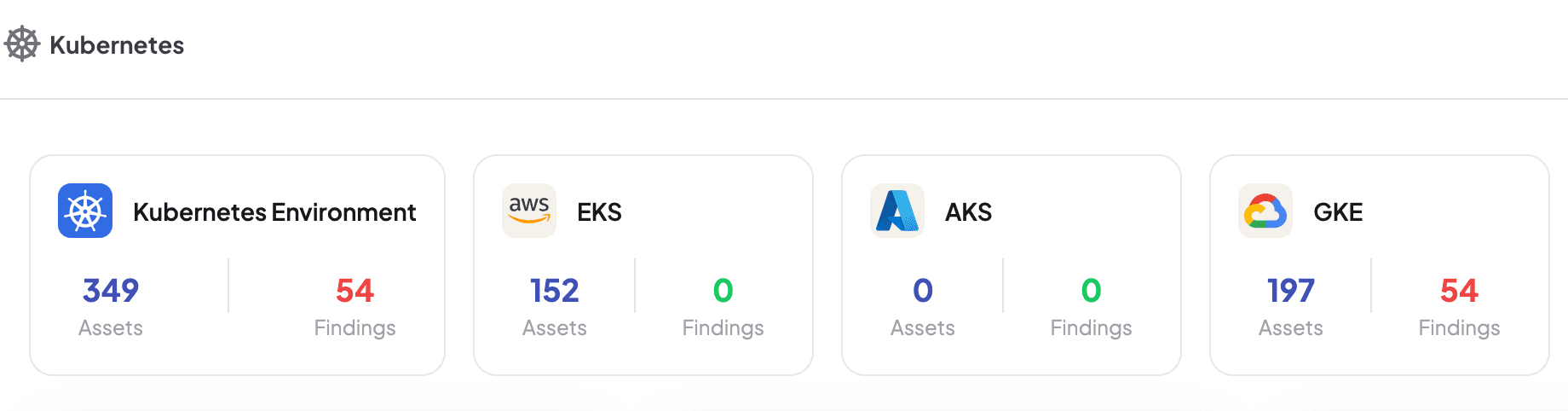
Unified visibility across EKS, AKS, and GKE
Continuous discovery of clusters, namespaces, pods, services, and workloads
Map Kubernetes components to the underlying cloud infrastructure
Identify where vulnerable container images are deployed—instantly
Continuous Monitoring
Continuous Kubernetes
Compliance Monitoring
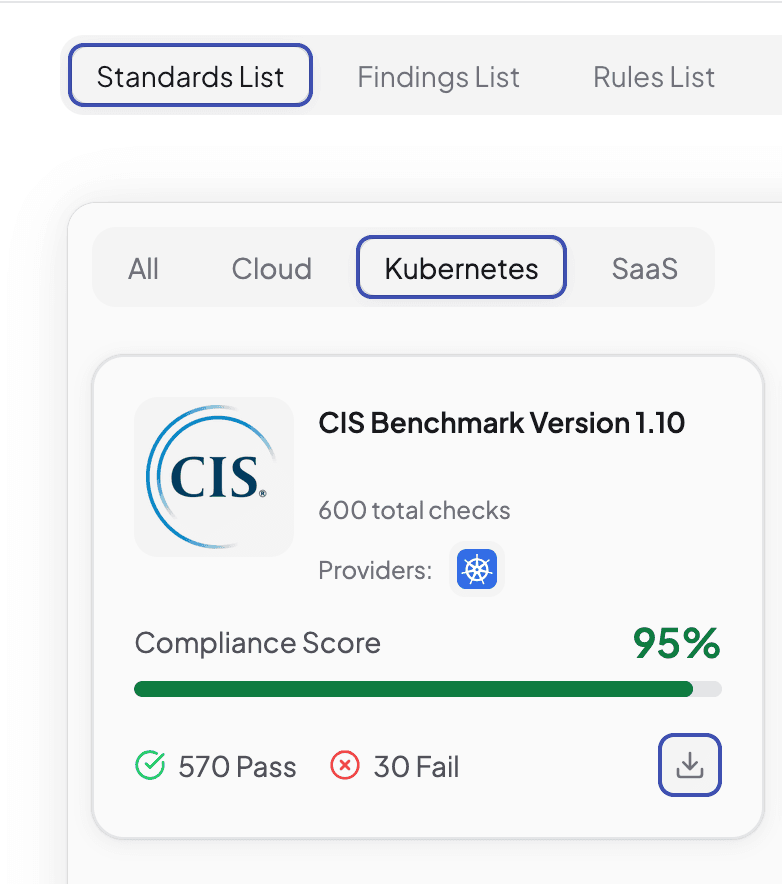
Suronex automates Kubernetes compliance checks using industry-recognized benchmarks and standards.
Continuous Posture Checks
Identify and remediate security issues in real-time with continuous compliance monitoring aligned with industry benchmarks.
CIS Benchmark Checks
Continuous CIS Kubernetes Benchmark checking with daily scans across all your clusters.
Automated Monitoring
Uninterrupted monitoring of API configurations, RBAC, and network segmentation.
Configuration Auditing
Proactive drift detection to identify deviations from secure baselines in real-time.
Compliance Reports
Generate audit-ready compliance reports equipped with detailed findings and guidance.
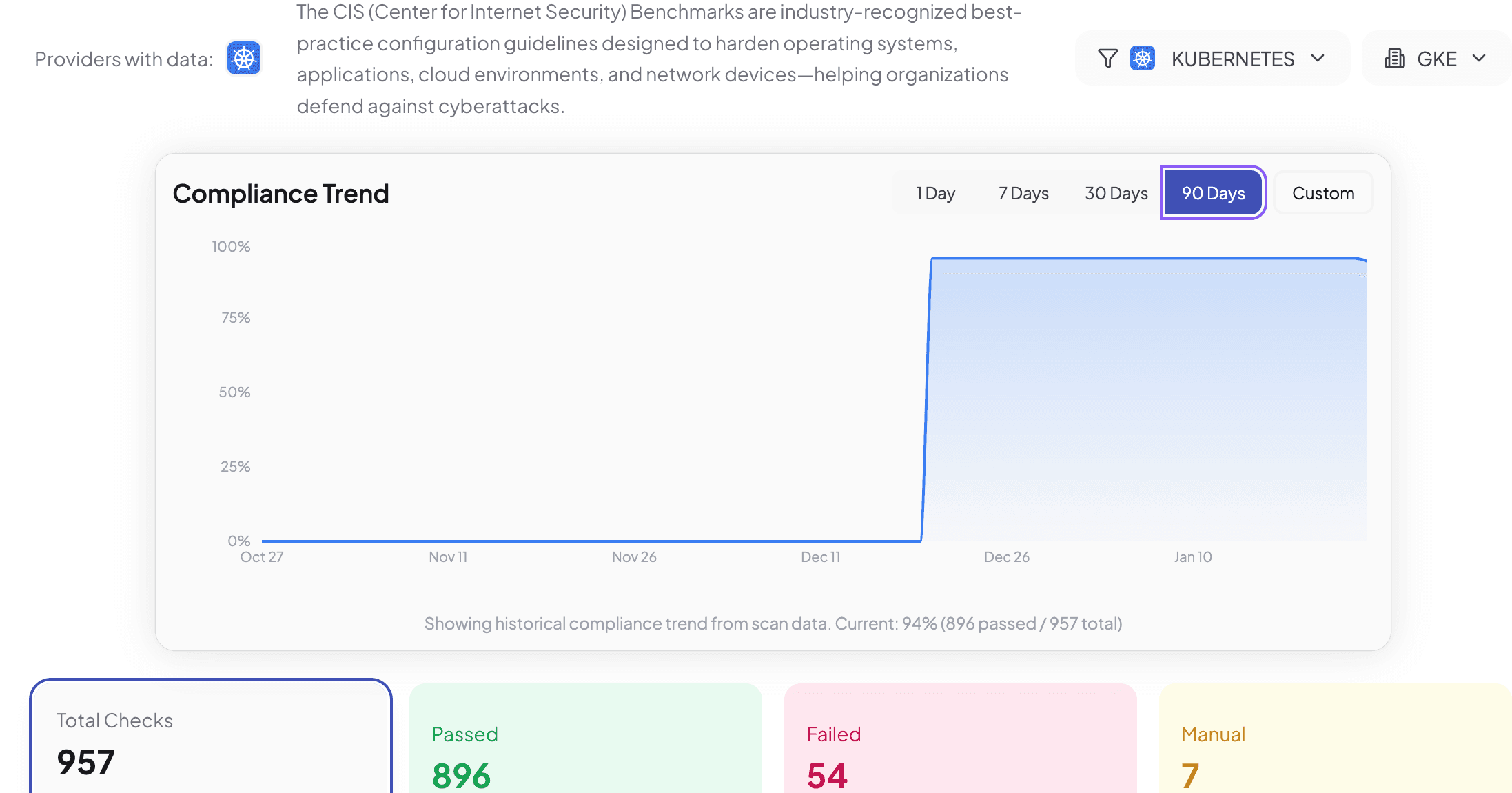
Compliance Trend Tracking
Monitor compliance trends over 90 days with detailed historical data showing improvement trajectory and compliance score evolution.
Real-Time Monitoring
Track configuration changes, API modifications, and RBAC updates as they happen across all your Kubernetes clusters.
Drift Detection
Automatically identify when cluster configurations deviate from security baselines and compliance requirements.
Audit Reports
Generate comprehensive compliance reports with detailed findings, evidence, and remediation guidance for auditors.
Risk Detection
Kubernetes Misconfiguration
& Risk Detection
Prevent real-world Kubernetes threats—without alert fatigue.
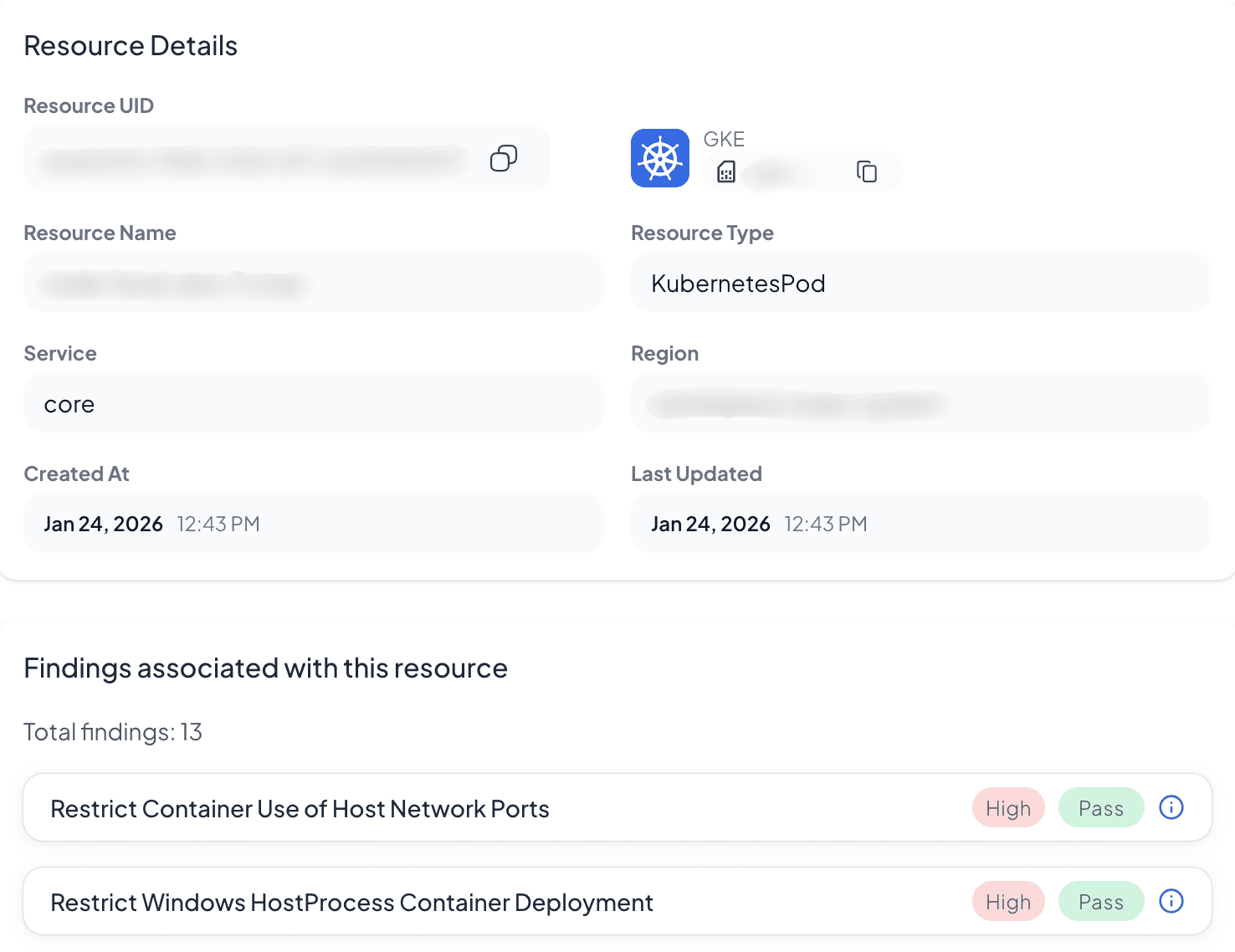
Detect misconfigurations across clusters, pods, containers, and services
Identify risky exposure paths caused by IAM, networking, and service misalignment
Eliminate false positives through contextual risk analysis
Prioritize findings based on exploitability and impact
Least Privilege
Secure Access with
Least Privilege
Suronex continuously evaluates Kubernetes identities and access controls.
Monitor RBAC roles, service accounts, and permissions
Identify over-provisioned access and privilege escalation risks
Enforce least-privilege access across workloads and teams
Built-In Compliance &
Policy Flexibility
Stay compliant with global and industry regulations while adapting to your internal standards.
Out-of-the-box policy templates for Kubernetes security
Support for CIS, ISO 27001, SOC 2, PCI DSS, GDPR, and more
Customize policies or import your own using a smart policy editor
Manage multiple compliance frameworks simultaneously
Audit Readiness
Faster Audits,
Less Manual Effort
Centralized Kubernetes asset inventory
One-click, audit-ready compliance reports
Clear evidence mapping for auditors and stakeholders
Reduce audit preparation time without slowing deployments
Cloud-Native Compliance
That Scales
Suronex enables organizations to secure Kubernetes by design—with continuous compliance, deep visibility, and intelligent remediation built into daily operations.
Protect your clusters. Govern your workloads. Stay compliant—continuously.
Cloud-Native Security & Compliance FAQs
Getting Started
Quick Deployment
Implementation Support
Pricing Models
Ready to Secure Your Kubernetes Environments?
See how Suronex automates Kubernetes compliance, reduces risk, and maintains continuous security posture.
Book a Demo